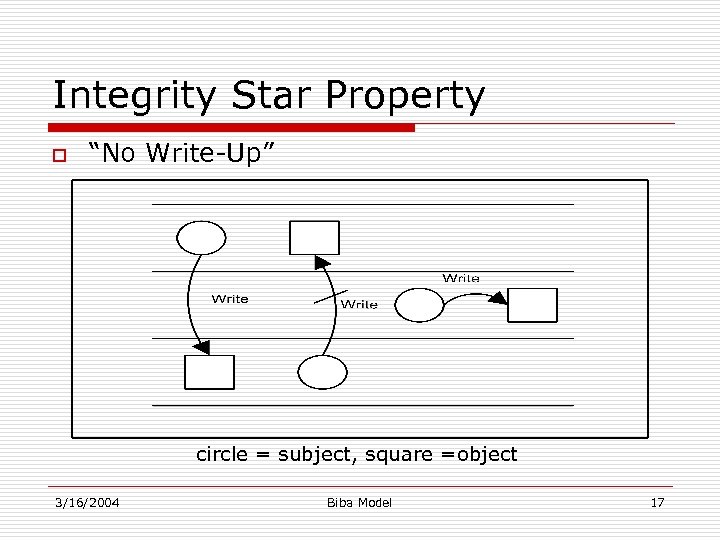
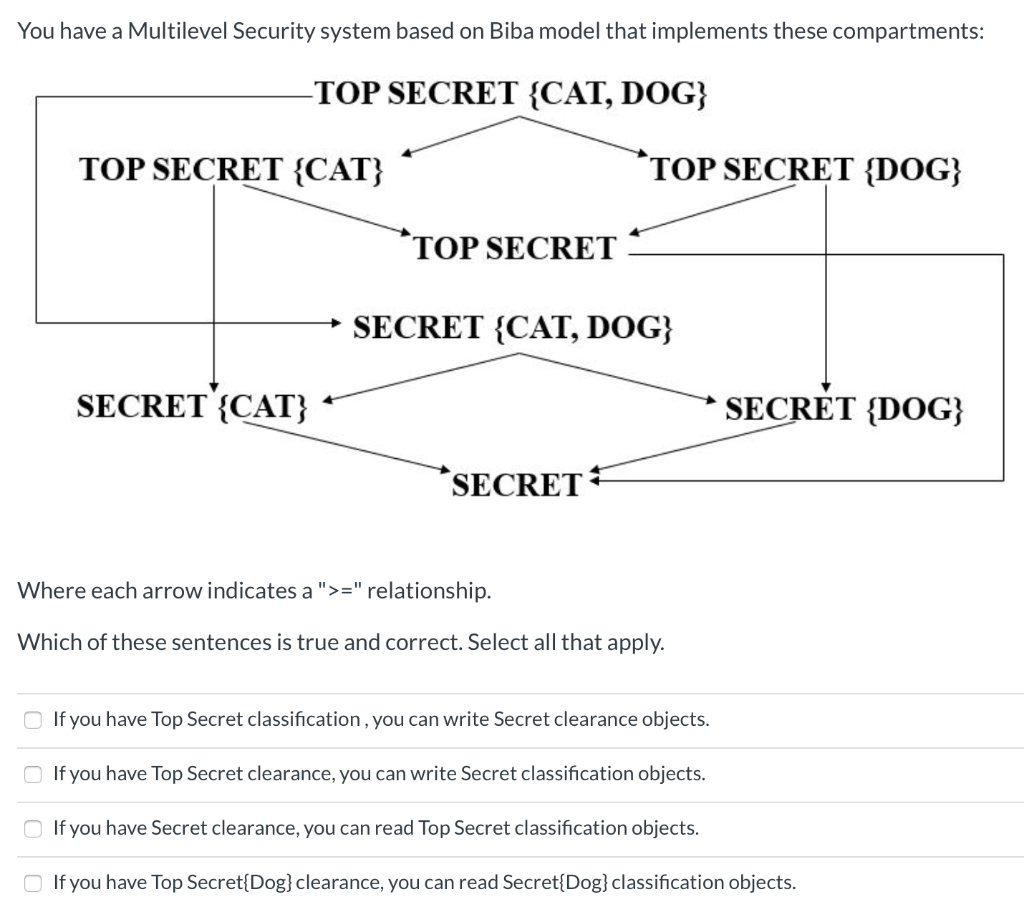
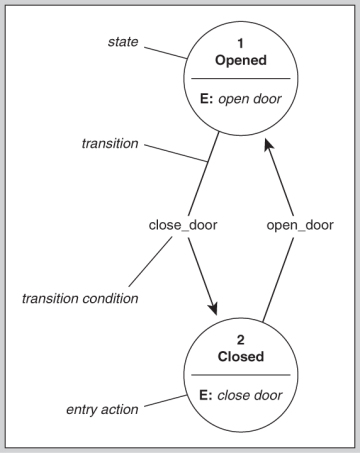
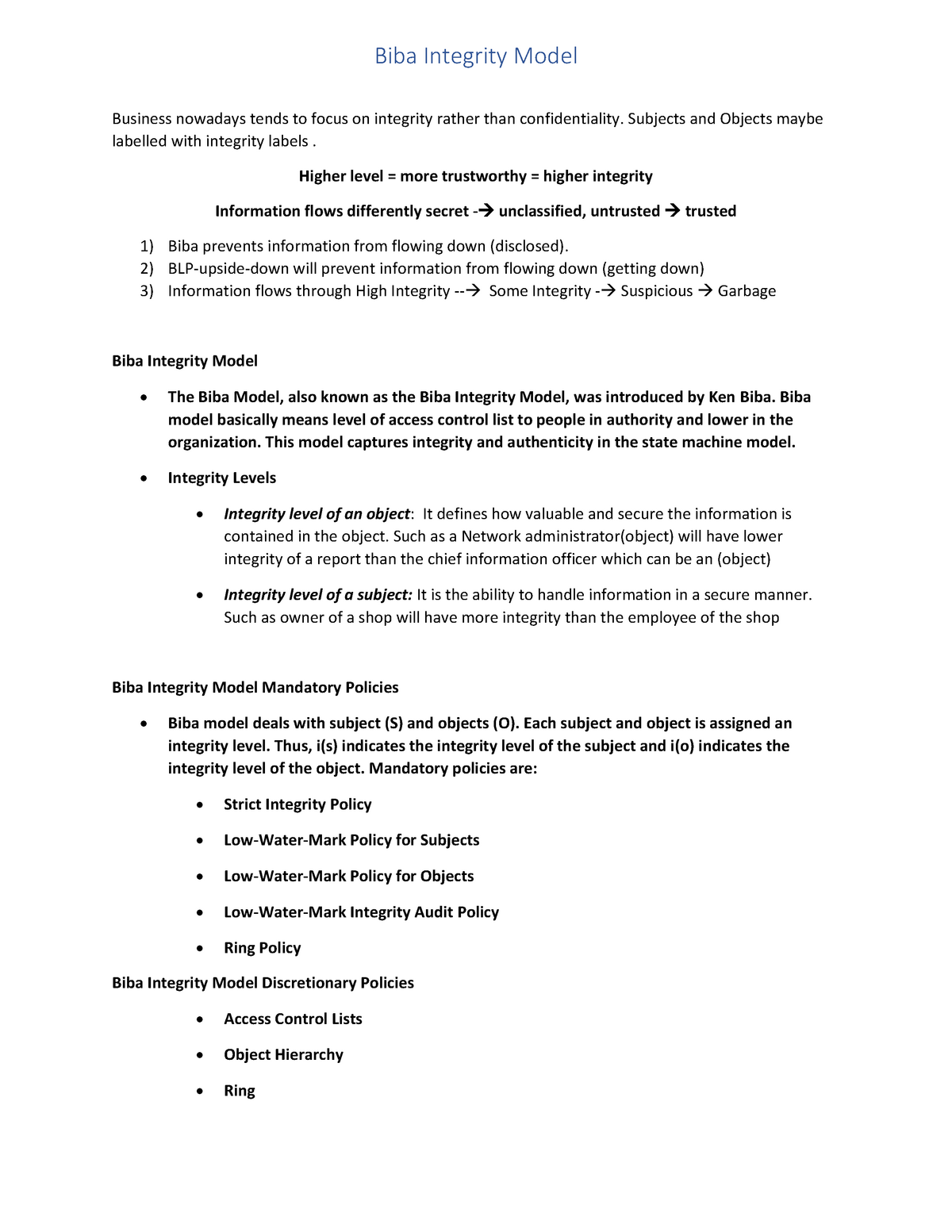
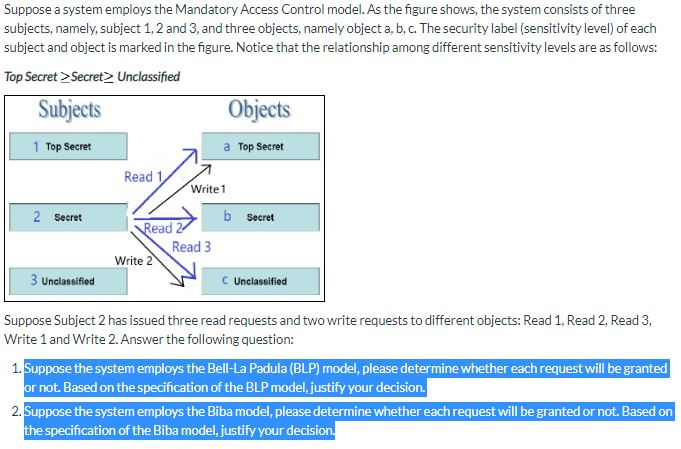
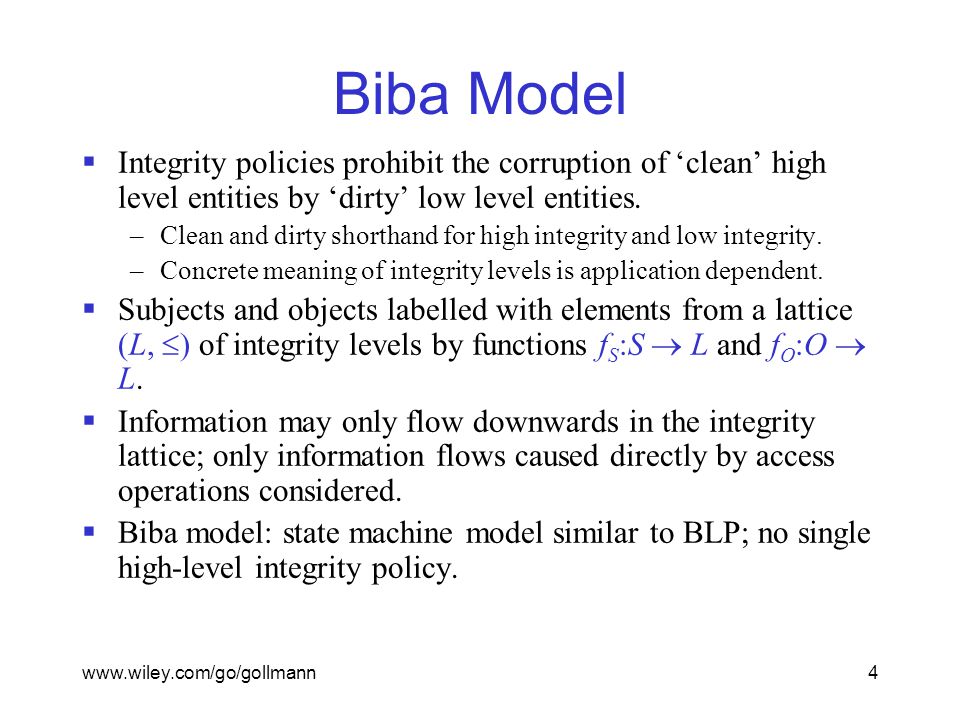
Integrity Models Biba Integrity Model (1977) Biba Model – ”no read down” Biba Model – ”no write up” Biba Model – i
Biba - Biba Integrity Model Presented by Nathan Balon Ishraq Thabet Biba Model 1 Computer Security Computer security is concerned with three aspects | Course Hero